Documentation Index
Fetch the complete documentation index at: https://docs.encord.com/llms.txt
Use this file to discover all available pages before exploring further.
Encord does not currently support Multi-Region Access Points for Azure.
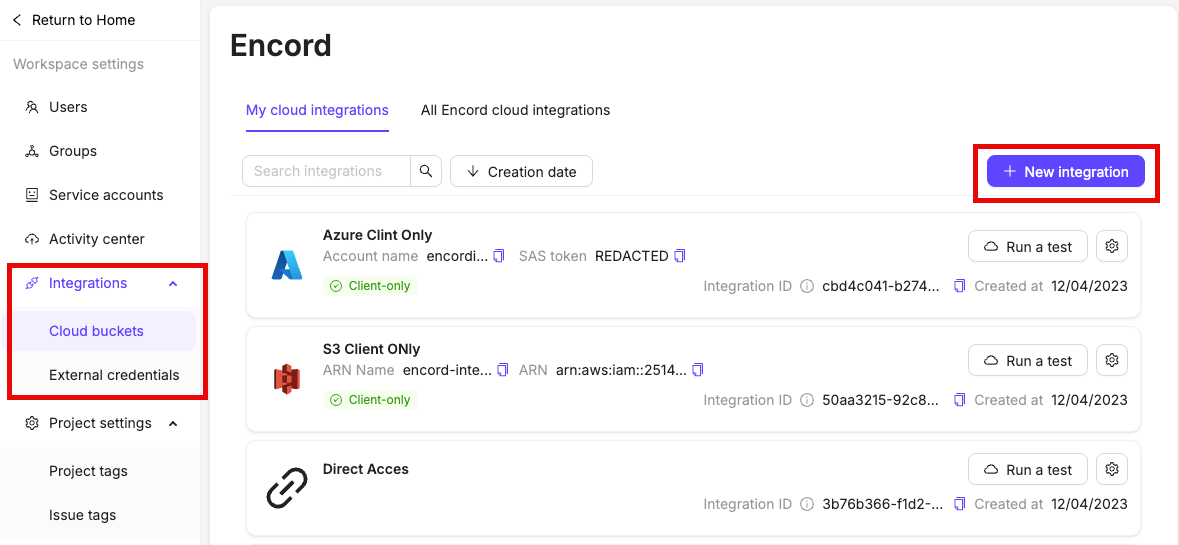
1. Set Up the Integration
- In Encord, navigate to the Integrations section and click the Add integration button.
- Click on Azure.
- Give your integration a meaningful name.
2. Register the Azure Storage Account
- Paste the name of your Azure storage account into Step 2 of the integration.

3. Select Authentication Type
Select your preferred method of authentication in Step 3 the Azure integration window.
4. Authenticate Azure
You can authenticate Azure in two different ways:Using a service principal to authenticate requires admin privileges for the Azure account.
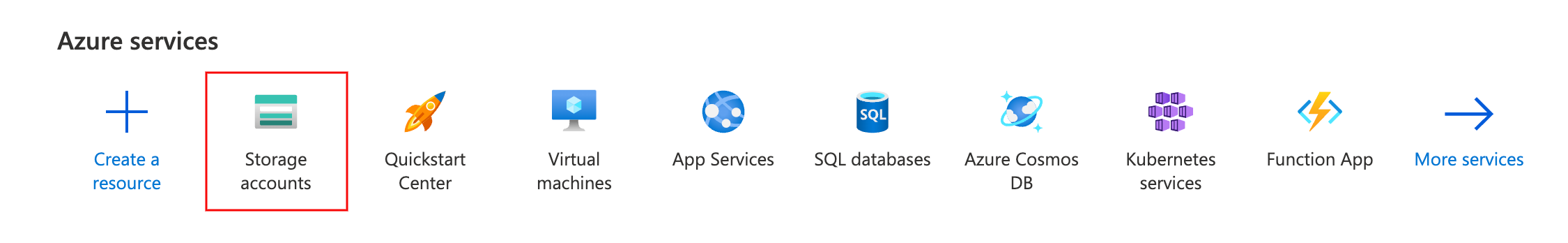
Method 1: Generate an Account-Level SAS
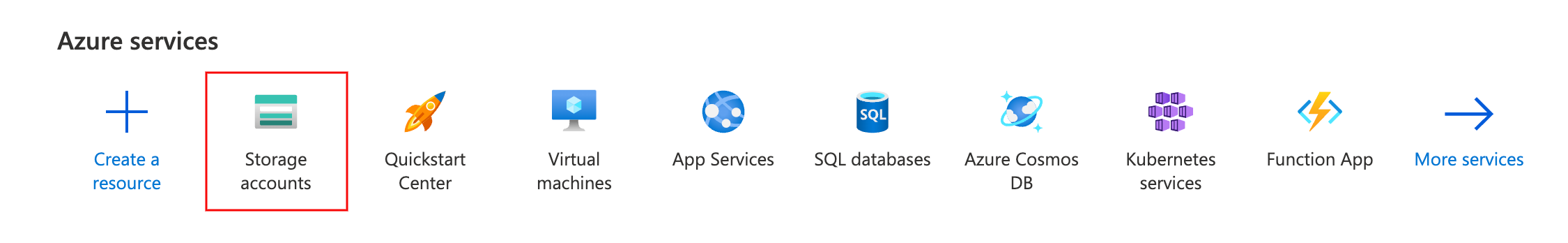
- In Azure, navigate to Storage Accounts under Azure services and select the storage account you wish to integrate.
- Next, click on Shared access signature in the Security + networking section.
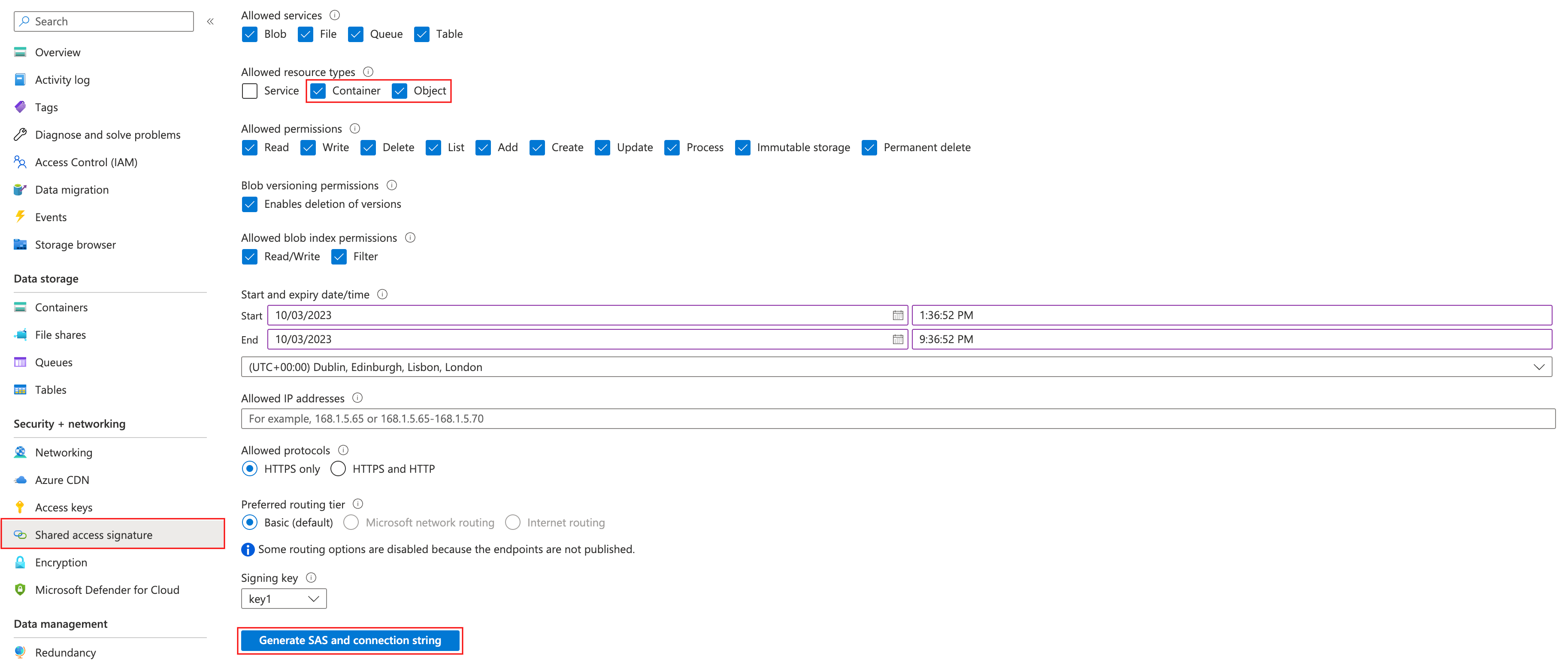
- You must check the Container and Object checkboxes under the Allowed resource types heading. Ensure you add the necessary permissions:
- Read (required)
- List (required)
- Write (recommended)
- Add (recommended)
- Create (recommended)
recommended permissions are necessary to use some of our more advanced features such as re-encoding data, and image sequences.
- Click Generate SAS and connection string when you are ready to generate your account-level SAS token.
- Paste the SAS token into Step 4 of the Azure integration window, in Encord.

Method 2: Use a Service Principal
Using a service principal to authenticate you require you to:Add the cord-integrator App to Azure Tenant
There are three different ways to add the cord-integrator app to Azure tenant:- Using a browser.
- Using Azure powershell.
-
By granting storage account and container permissions to
cord-integrator.
You need to have admin privileges for your Azure account to authenticate via a service principal.
Add the cord-integrator App in a Browser
You can add the cord-integrator application in the Settings of the Encord app. If logged in to the Encord platform, you are redirected to the ‘Azure integration’ screen after the application was successfully added.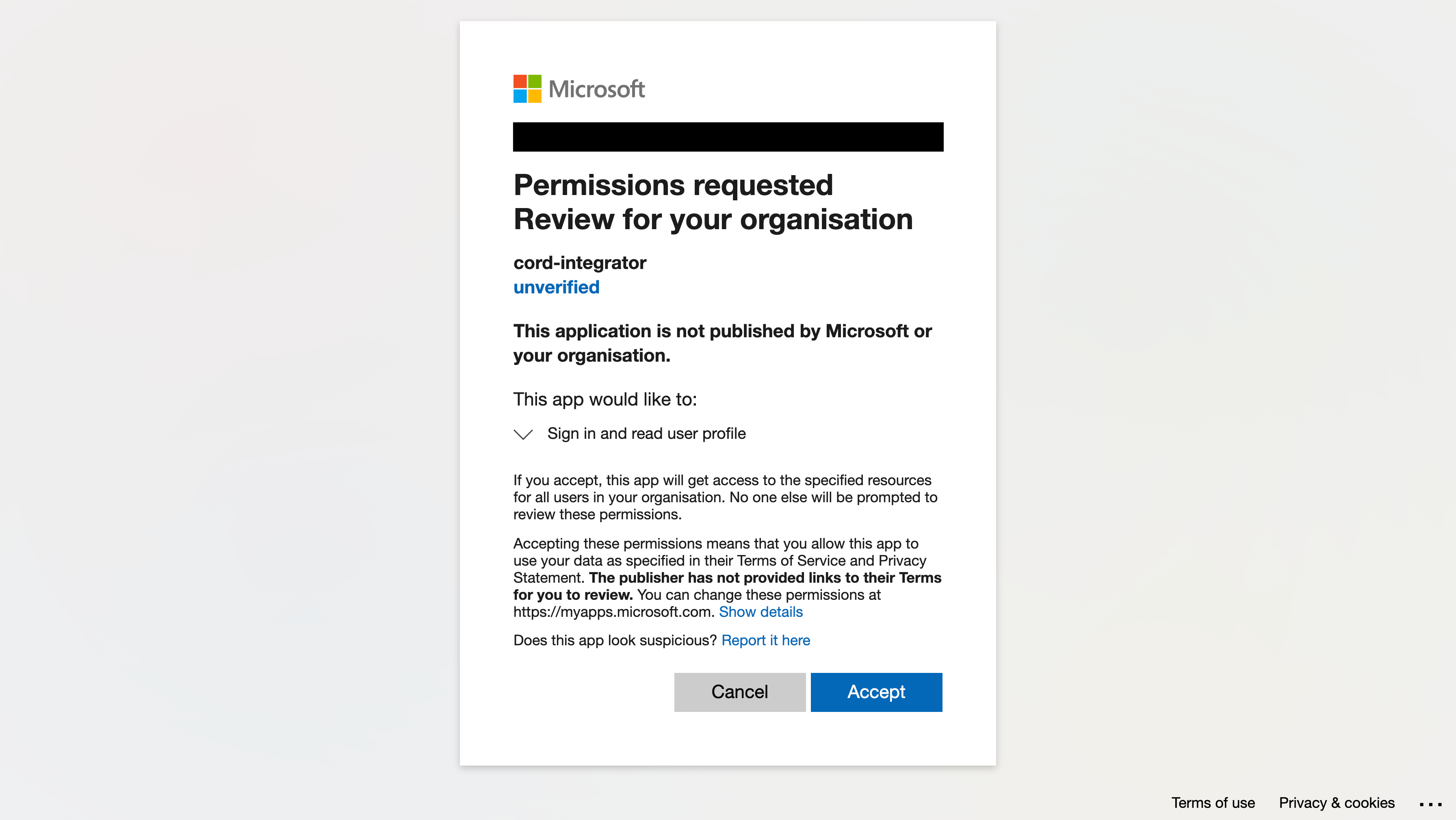
Add the cord-integrator app via Azure Powershell
Grant Storage Account and Container Permissions to cord-integrator
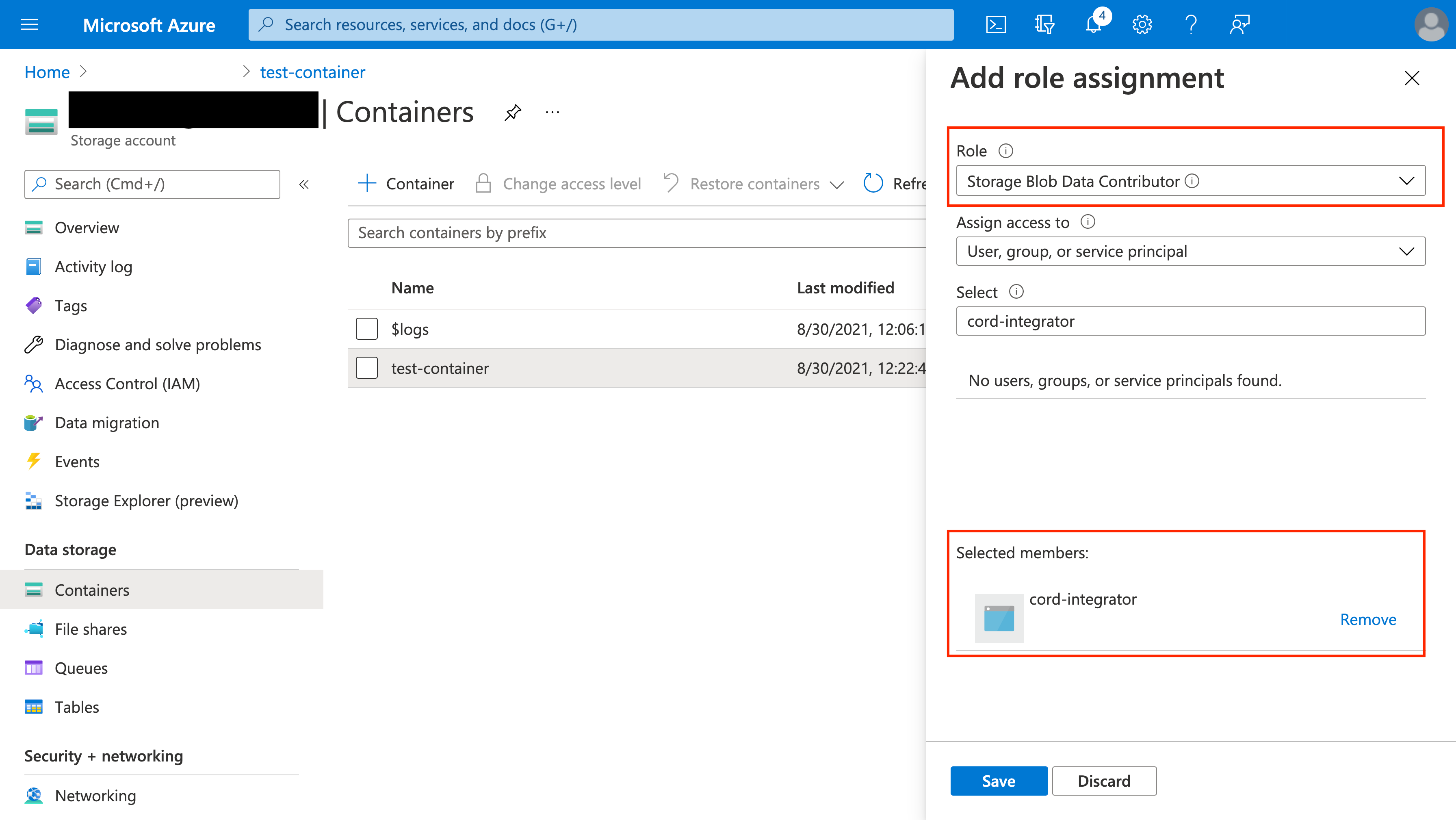
The cord-integrator must be granted two types of permissions in order to function:- The Storage Blob Data Contributor role at the container level
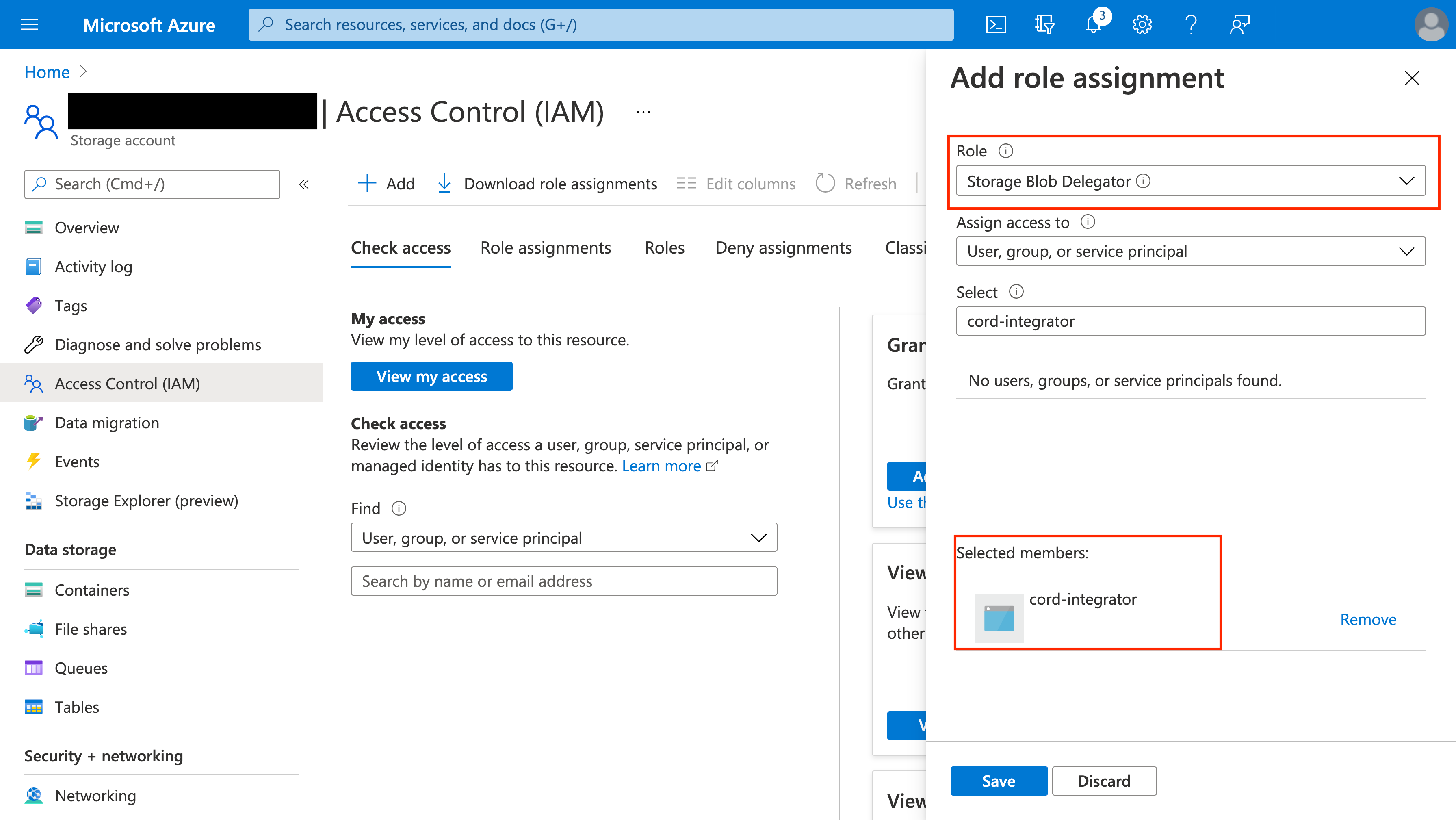
- The Storage Blob Delegator role at the storage account level
Find your Azure tenant ID
You can find the Azure Tenant ID in the Active Directory overview of your Azure project.

5. Create a CORS Configuration in Azure
A CORS configuration must be applied to the Azure storage account you want to integrate with Encord. This enables Encord to request resources from the specified service account using a browser.- Navigate to the Resource Sharing (CORS) section under Settings of your storage account.
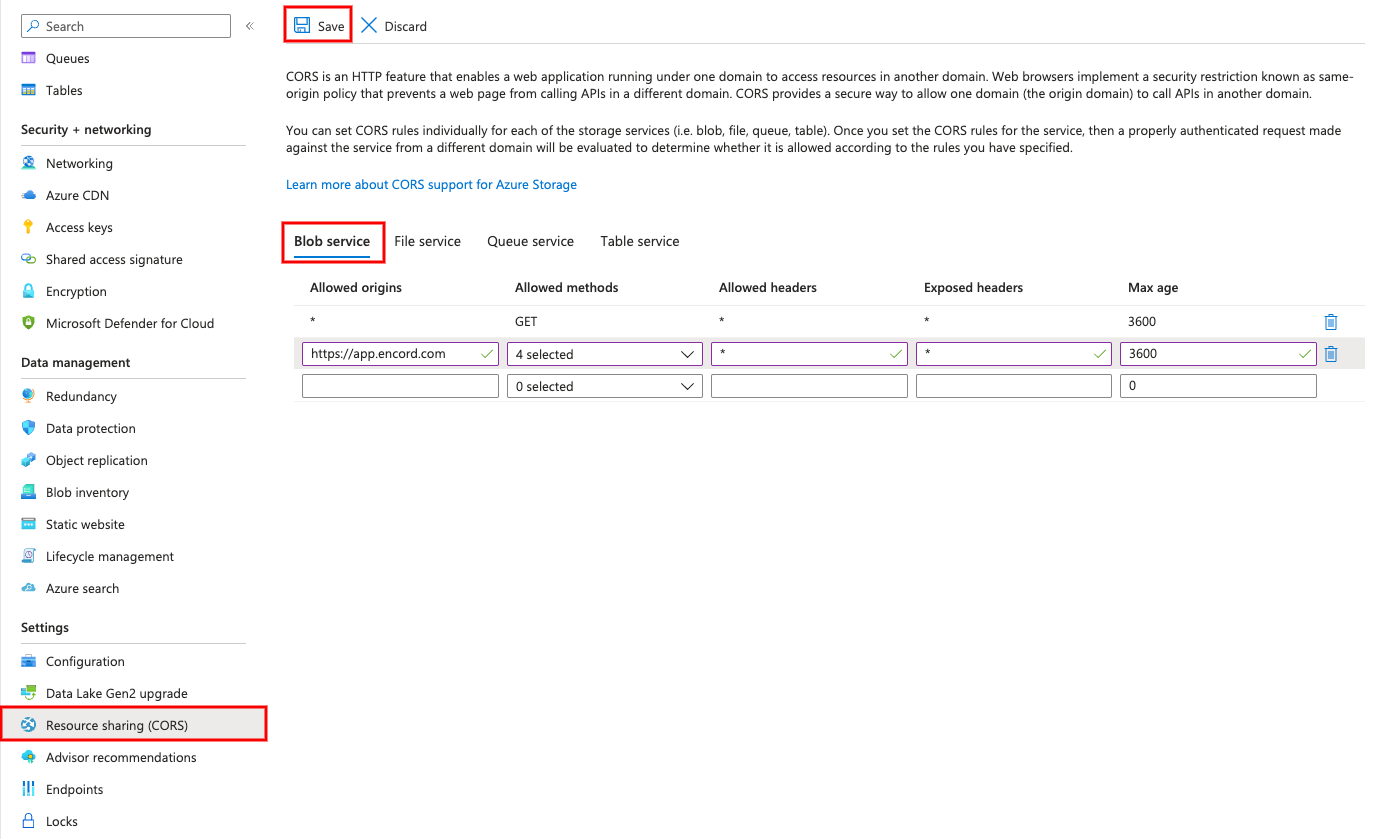
- Input the following values in the Blob service tab of Resource Sharing (CORS) page:
- Global
- EU
- US
| Allowed origins | Allowed methods | Allowed headers | Exposed headers | Max age |
|---|---|---|---|---|
https://app.encord.com | GET, POST, OPTIONS, PUT | * | * | 3600 |
https://api.encord.com | GET, POST, OPTIONS, PUT | * | * | 3600 |
https://app.us.encord.com | GET, POST, OPTIONS, PUT | * | * | 3600 |
https://api.us.encord.com | GET, POST, OPTIONS, PUT | * | * | 3600 |
- Click Save to save the CORS configuration.
- Click Create to finish setting up the integration, in Encord.
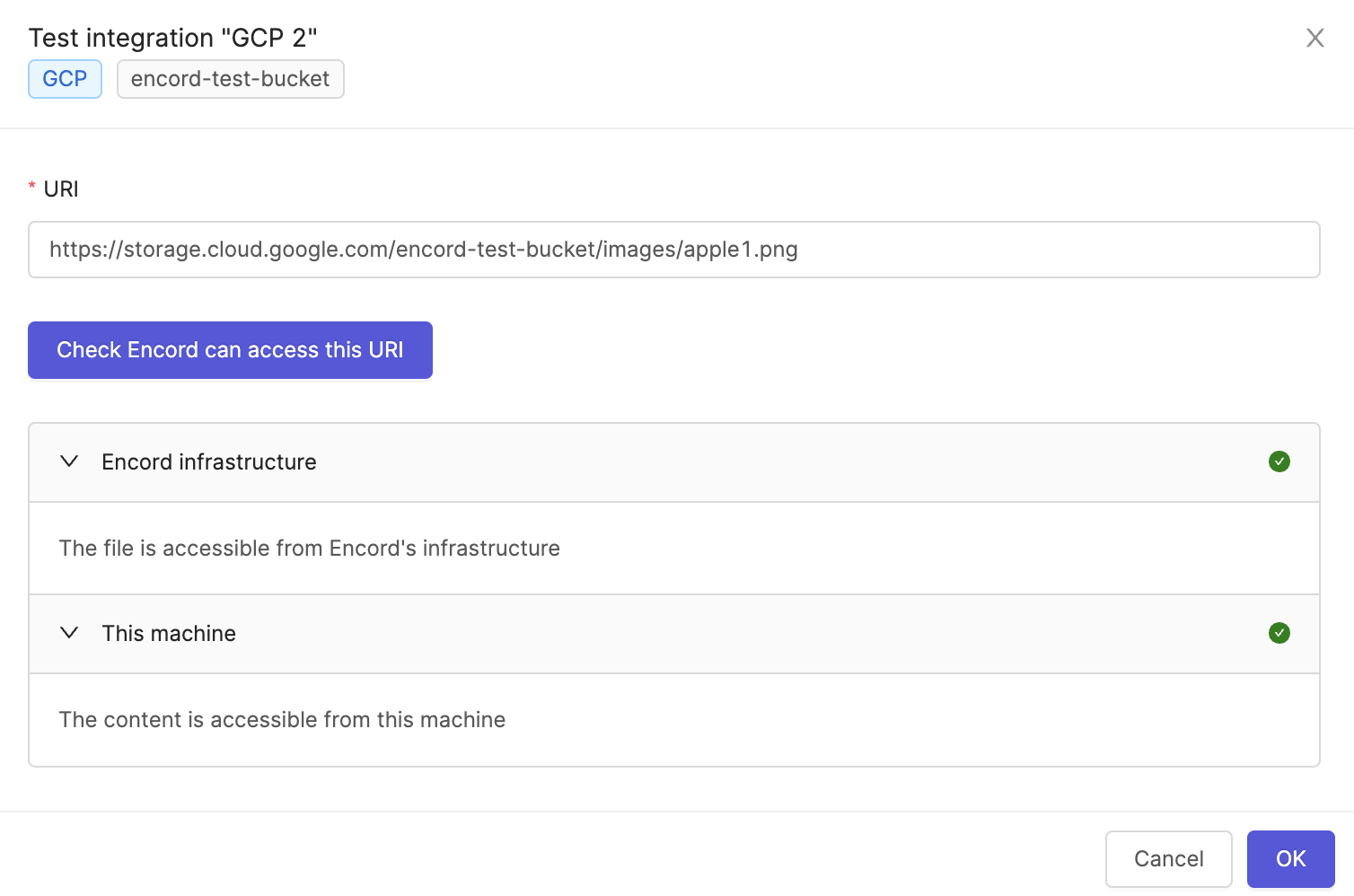
6. Test Your Integration
Click the Run a test button on the integration, to test that the integration works.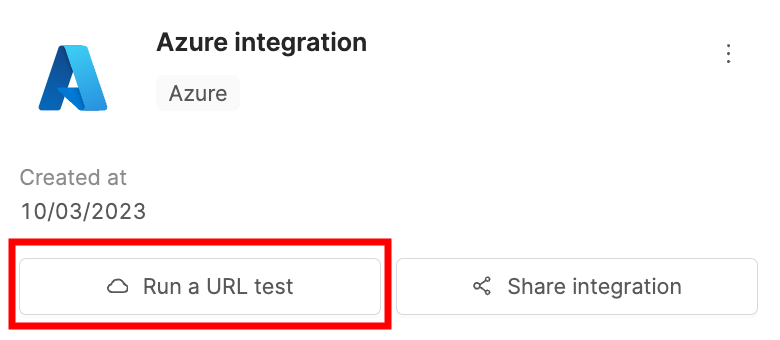
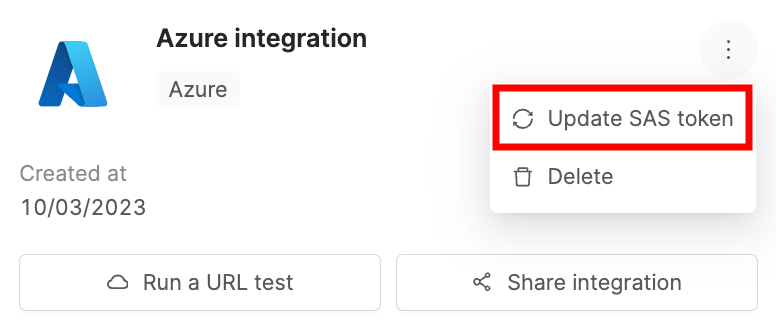
Updating Expired Account-Level SAS Tokens
This section is only applicable if you used an account-level shared access token to authenticate.
- Click the three dots icon on your Azure integration.
- Click Update SAS token.
- In Azure, navigate to Storage Accounts under Azure services and select the storage account you wish to update the token for.
- Click on Shared access signature in the Security + networking section.
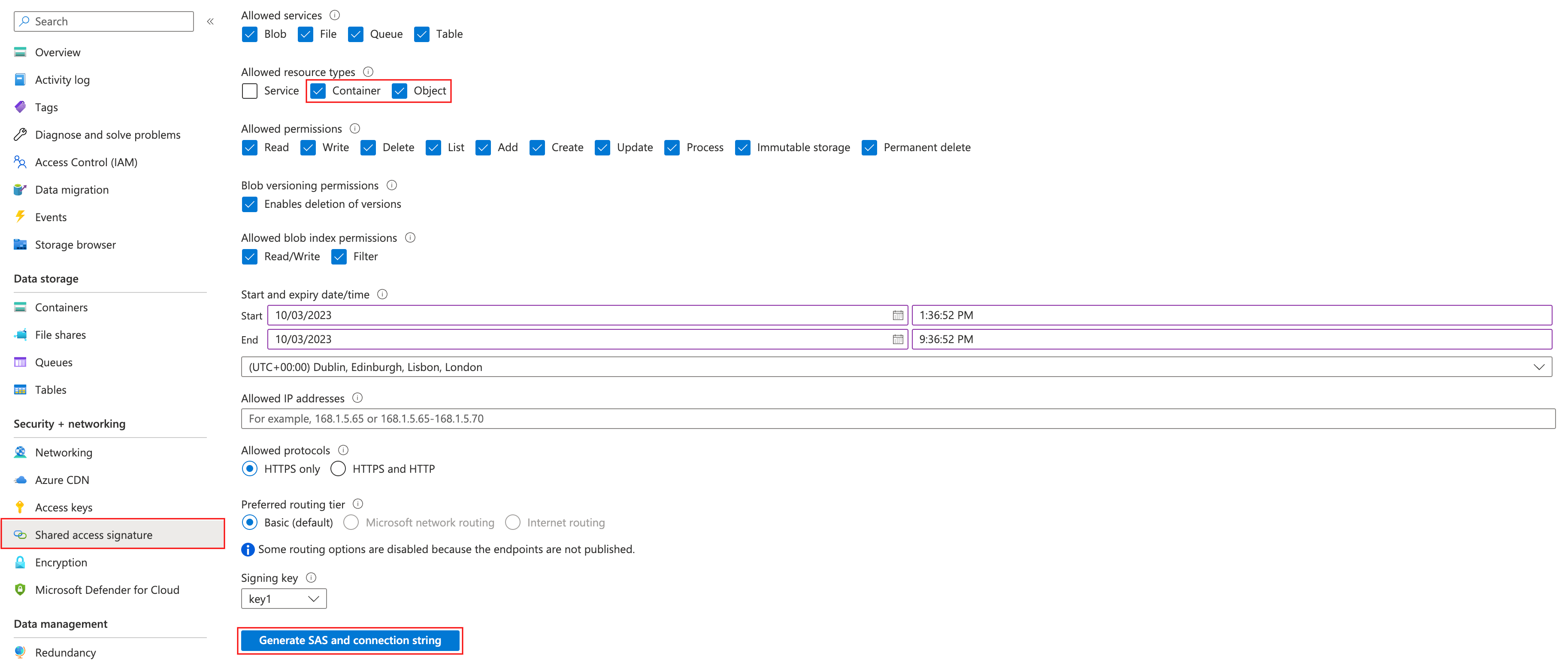
- You must check the Container and Object checkboxes under the Allowed resource types heading. Ensure you add the necessary permissions:
- Read (required)
- List (required)
- Write (recommended)
- Add (recommended)
- Create (recommended)
recommended permissions are necessary to use some of our more advanced features such as re-encoding data, and image sequences.
- Click Generate SAS and connection string to generate a new account-level SAS token.
- Paste the new SAS token, in Encord.

